This article describes how to inspect NetFlow which has been collected using nfcapd(1) from the nfdump toolkit with nfdump(1)
Background
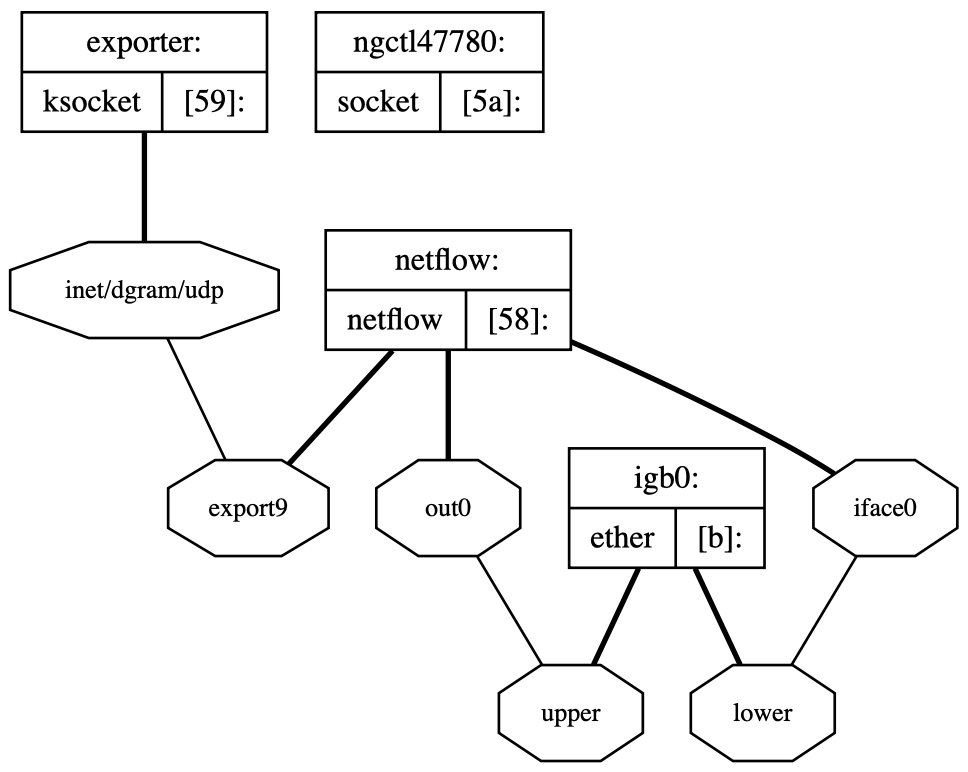
In the article Collect and save NetFlow data with FreeBSD I describe what NetFlow is and how to collect and store NetFlow using FreeBSD. But without an efficient way to inspect the data it is practically useless.
Using nfdump
nfdump uses a filtering syntax that is similar to bpf-syntax (the one tcpdump uses). This means that everyone familiar with tcpdump could get started rather quickly. For example:
$ nfdump -R netflow/ -o tstart -o extended 'host 172.18.37.34 and port 53'
Often you want to sort on a specific metric, for example “which hosts have the most traffic on port 53”, this can be done using the statistics option -s
$ nfdump -R netflow/ -s ip/bytes 'port 53'
Another really useful feature is aggregation. This can be used to aggregate all flow records over a specific set of parameters. The below example uses option -A to aggregate all flows where srcip and dstip are the same and then filters out a specific host of interest. In other words “Who has been talking to host x”
$ nfdump -R netflow/ -A srcip,dstip -n 20 'host x'
If you want to see flows for a specific timeframe you can use the -t option like this
$ nfdump -R netflow/ -s ip/bytes -n 20 -t 2019/01/21-2019/01/22
You can also change the output format to suit your needs. The formatting syntax are a little bit unintuitive (at least I haven’t seen it before) so you may have to reference the manual
$ nfdump -R /data/netflow/ -o tstart -o 'fmt:%ts %pr %sap %dap'
Flow records by them self have no sense of sessions and are unidirectional. If you want to see data for bidirectional flows you can tell nfdump to aggregate on bidirectional flows using -b or -B
$ nfdump -R netflow/ -A srcip,dstip -n 20 -B 'host x'
But please note that it is a guess.
This was a short introduction on how to inspect netflow data with nfdump. Please leave a comment if you have any questions or suggestions.